George Weisgerber

FinOps 2025: Trends and ITAM Synergy
Reaching new heights with FinOps in 2025! Explore the latest trends shaping the FinOps landscape and discover how IT Asset Management (ITAM) can elevate your strategy.
This webinar will highlight key insights and practical approaches to optimizing IT and financial operations in the year ahead. Designed for ITAM, procurement, and finance professionals, it provides the tools you need to stay ahead in 2025.
Learn how to align financial and operational goals, maximize value, and drive success in a rapidly evolving digital environment. Don’t miss this opportunity to enhance your FinOps expertise and plan for the future!
How to fit ITAM into your organization’s IT Value Story
This session enables technology leaders to build a strong value story, advance their strategic agenda, and make ITAM more relevant to the wider organization.
Demonstrating ITAM value is about making your work relevant to, and understood by, the wider organization. Each organization and functional leader is unique, but value is always determined by the stakeholder or consumer, not the provider or producer.
Join us to discuss how successful ITAMs and SAMs are crafting value stories that secure more funding and elevate IT’s standing in the wider organization.
BitRaser
IAITAM Provider Member BitRaser offers a comprehensive software portfolio, including Data Erasure, Diagnostics, and Erasure Verification tools, which are ideal for companies striving for compliance. As a certified data erasure solution, the BitRaser Drive Eraser tool...
Determining a Software Compliance Position
Maybe there is a renewal coming, we heard there may be a licensing issue through the grapevine, or we are just being proactive. There are plenty of reasons to know our compliance position for a piece of software. At the point we decide we want to know our position, what next? Let’s talk about approaching determining a compliance position. Let’s spend some time talking through what works well, what maybe hasn’t worked well, and some things we can do going forward to be more confident (and accurate) in our compliance and reporting.
THE SAP ERP Transformation ERA | A decade of S/4HANA
As 2027 draws near, SAP customers are faced with a critical decision: transition to S/4HANA or extend their mainstream maintenance for ECC by three more years. Regardless, change is inevitable. This session will delve into the various options available, negotiation techniques and control mechanism that are meant to support you secure your future, whether you’re already on S/4HANA or still considering the migration
A sneak peek and how Microsoft is implementing Intelligent licensing into our SAM program
Microsoft is leveraging AI in its Software Asset Management program to significantly enhance efficiency in license management and drive customer satisfaction. By integrating AI-driven solutions, Microsoft can accurately track and manage software licenses, ensuring compliance and optimizing usage. The intelligent license models enable quick responses to the license needs of internal users, reducing downtime and improving productivity. This proactive approach not only streamlines the management process but also ensures that users have timely access to the necessary software, ultimately leading to higher satisfaction and more efficient operations. Learn a little of this and take an opportunity to see the overall program at work during the ACE Conference.
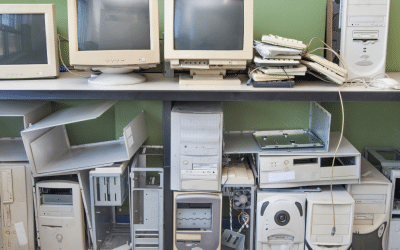
Data or Not? How to identify security risks in IT Assets
In this presentation, we will cover some trends in IT Assets and data-bearing devices. We will then have an interactive session in which we will show pictures of various IT assets and ask the webinar participants to vote via chat on whether or not they contain data. Finally, we will talk about some best practices and tools to reduce the risk of a data breach.
Workflow Automation – The Future of SAM
Workflow Automation is being embraced by organizations of all sizes because it offers clear benefits of reducing errors, increasing efficiency, improving consistency and collaboration, reducing costs, and enhancing data security. We will discuss how SAM can drive workflow automation within your organization with example workflows such as employee on-boarding and off-boarding; software requests; optimizing SaaS and Subscription software costs based on usage, and entering purchase records.
CDR Global Inc.
IAITAM Provider Member At CDR Global, we are dedicated to delivering secure, sustainable, and value-driven IT Asset Disposition (ITAD) and lifecycle services. We prioritize data security, environmental responsibility, and financial returns, ensuring our clients...
How to Make IT Asset Management a Strategic Advantage, Not Just an Operational Necessity
ITAM is more than tracking hardware and software – it’s a strategic function! By leveraging ITAM data, collaborating with key departments, and aligning with business goals, organizations can reduce risks, optimize technology investments, and unlock long-term value.